- 6 Posts
- 5 Comments

 1·6 months ago
1·6 months agoKeycloak seems complicated, but it’s actually not that complicated if you use it for simple OIDC provider.
Just create a new realm, then go to client -> create. Enter your client-id, with openid-connect as protocol. Then, set access type to “confidential”, set valid redirect uri to “https://<your app>” (or even “https://*” if you’re lazy and want to use it on multiple apps). Then hit save and go to the credential tab to copy your client secret. Then head to “users” menu to start adding users to your realm.
That’s the basic setup which should be good for home use. The good thing about keycloak is, as you grow your homelab, whatever stuff you may need later can be provided by keycloak. Want some users to have access to app A, but not app B? 2 factor auth? Allow users to login with google account? Heck, allow users to login with another sso provider (chaining)? You can do pretty much anything.

 1·7 months ago
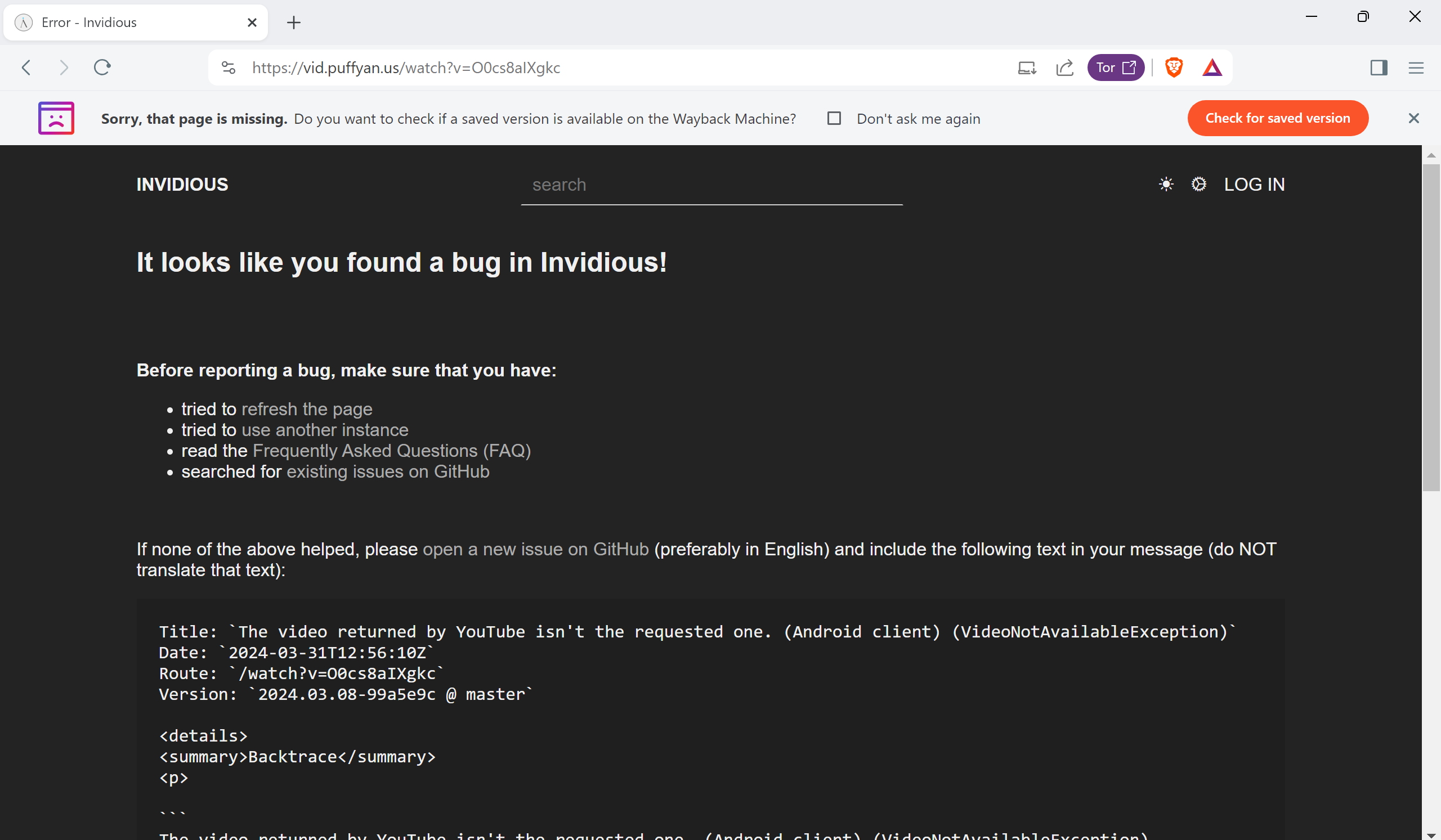
1·7 months ago* zoom in on the error message
Yep, of course it’s Nvidia.
Should I setup DKIM, DMARC, SPF and reverse IP lookup?
This is no brainer to setup using mailcow. Just need to copy paste the provided TXT values from mailcow ui into your dns entries.
Mailcow is fantastic and very easy to deploy. I highly recommend it.

 1·1 year ago
1·1 year agoAccording to Hwang, the company now formerly known as Twitter did offer “an alternative handle with the history of the @x account” so that his original account, complete with its posts and followers, could live on and continue to be used.
What short, catchy username did Musk’s company change Hwang’s handle to? @x12345678998765.
You can’t make this shit up. God damn!




Due to how federation works, downvotes are actually somewhat public because instance owners can query them in lemmy database, though instance owners probably won’t tell you if you ask due to privacy reason. If you’re interested in something like this, you can run your own instance.